Prerequisites, Limitations, and Caveats
Before configuring your workloads to use SecureConnect, review the following prerequisites and limitations, and consider the following caveats.
PKI Certificates with SecureConnect
The following prerequisites and limitations apply when configuring SecureConnect to use certificates:
- You must have a PKI infrastructure to distribute, manage, and revoke certificates for your workloads. The PCE does not manage certificates or deliver them to your workloads.
- The PCE supports configuring only one global CA ID for your organization.
- The VEN on a workload uses a Certificate Authority ID (CA ID) to authenticate and establish a secure connection with a peer workload.
Connected workloads must have CA identity certificates signed by the same root certificate authority. When workloads on either end of a connection use different CA IDs, the IKE negotiation between the workloads will fail and the workloads will not be able to communicate with each other.
VEN Versions
To use PKI certificates with SecureConnect, your workloads must be running VEN version 17.2 or later.
Existing IPsec Configuration on Windows Systems
Installing a VEN on a Windows system does not change the existing Windows IPsec configuration, even though SecureConnect is not enabled. The VEN still captures all logging events (event.log, platform.log) from the Windows system that relate to IPsec thereby tracking all IPsec activity.
Maximum Transmission Unit (MTU) Size
IPsec connections cannot assemble fragmented packets. Therefore, a high MTU size can disrupt SecureConnect for the workloads running on that host.
Illumio recommends setting the MTU size at 1400 or lower when enabling SecureConnect for a workload.
Ports
Enabling SecureConnect for a workload routes all traffic for that workload through the SecureConnect connection using ports 500/UDP and 4500/UDP for NAT traversal and for environments where ESP traffic is not allowed on the network (for example, when using Amazon Web Services). You must allow 500/UDP and 4500/UDP to traverse your network for SecureConnect.
Unsupported SecureConnect Usage
SecureConnect is not supported in the following situations:
- SecureConnect cannot be used between a workload and unmanaged entities, such as the label “Any (0.0.0.0/0 and ::/0” (such as, the internet).
- SecureConnect is not supported on virtual services.
- SecureConnect is not supported on workloads in the Idle policy state. If you enable it for a rule that applies to workloads that are in both Idle and non-Idle policy states, you can impact the traffic between these workloads.
- SecureConnect is not supported on AIX and Solaris platforms.
SecureConnect Encryption
When you configure workloads to use SecureConnect be aware of the following caveat.
SecureConnect encrypts traffic for workloads running in all policy states except Idle.
Performance
The CPU processing power that a workload uses determines the capacity of the encryption. The packet size and throughput determine the amount of power that is required to process the encrypted traffic using this feature.
In practice, enabling SecureConnect for a workload is unlikely to cause a big spike in CPU processing or a decrease in network throughput. However, Illumio recommends benchmarking performance before enabling SecureConnect and comparing results after enabling it.
SecureConnect Host-to-Host Encryption
When you configure workloads to use SecureConnect be aware of the following caveat.
SecureConnect encrypts traffic between workloads on a host-to-host basis. Consider the following example.
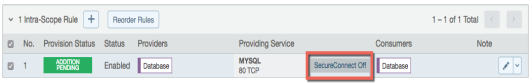
In this example, it appears that enabling SecureConnect will only affect MySQL traffic. However, when you enable SecureConnect for a rule to encrypt traffic between a database workload and a web workload over port 3306, the traffic on all ports between the database and web workloads is protected by IPsec encryption.
Use Pre-Shared Keys with SecureConnect
SecureConnect includes the option of using pre-shared keys (generated by the PCE) or client-side PKI certificates for IKE authentication.
You can configure SecureConnect to use pre-shared keys (PSKs) to build IPsec tunnels that are automatically generated by the PCE. SecureConnect uses one key per organization. All the workloads in that organization share the one PSK. SecureConnect uses a randomly generated 64-character alpha-numeric string, for example:
c4aeb6230c508063db3e3e1fac185bea9c4d17b4642a87e091d11c9564fbd075When SecureConnect is enabled for a workload, you can extract the PSK from a file in the /opt/illumio directory, where the VEN stores it. You cannot force the PCE to regenerate and apply a new PSK. If you feel the PSK has been compromised, contact Technical Support.
Illumio customers accessing the PCE from the Illumio cloud can have multiple Organizations. However, the Illumio PCE does not support multiple Organizations when you have installed the PCE in your datacenter.
Configure SecureConnect for Pre-shared keys
To configure SecureConnect to usepre-sharedkeys, follow these steps:
- From the PCE navigation menu, choose Infrastructure > SecureConnect Gateways.
- On the SecureConnect Gateways page, click Add.
|
Section |
Feature |
Description |
|---|---|---|
|
GENERAL |
Name of the SC Gateway |
Type the name of the Gateway (required) |
|
|
Description |
Type the description of the Gateway |
| Gateway IP Address | Type the IP address of the Gateway | |
| VPN CONFIGURATION | Authentication | Choose between the Certificate and a pre-shared key |
| Certificate (rsa-sig) | ||
| Pre-shared Key | ||
| Pre-shared Key | Enter the key ID | |
| Idle Timeout (minutes) | e.g. 5 | |
| Rules | Rules include Protected IP list. Scope is expanded to all workloads when not restricted to specific labels. |
Use Client-side PKI Certificates with SecureConnect
SecureConnect allows you to use client-side PKI certificates for IKE authentication and IPsec communication between managed Workloads. The PCE supports configuring only one global CA ID for your organization. Configuring SecureConnect to use certificates applies the setting to All Roles, All Applications, All Environments, and All Locations.
Configuring SecureConnect to use PKI certificates in the global Security Settings page does not manage certificates for your organization or deliver them to your Workloads.
You must independently set up certificates on your Windows and Linux Workloads. For information, see Requirements for Certificate Setup on Workloads.
If you have a certificate management infrastructure in place, you can leverage it for IKE authenticate between workloads because it provides higher security compared to using pre-shared keys (PSKs).
Certificate-based SecureConnect works for connections between Linux workloads, between Windows workloads, and between Linux and Windows workloads.
The IPsec configuration uses the certificate with the distinguished name from the issuer field that you specify during PCE configuration for IKE peer authentication.
Configure SecureConnect for Pre-shared keys
To configure SecureConnect to use a PKI certificate, follow these steps:
- From the PCE navigation menu, choose Infrastructure > SecureConnect Gateways.
- On the SecureConnect Gateways page, click Add.
|
Section |
Feature |
Description |
|---|---|---|
|
GENERAL |
Name of the SC Gateway |
Type the name of the Gateway (required) |
|
|
Description |
Type the description of the Gateway |
| Gateway IP Address | Type the IP address of the Gateway | |
| VPN CONFIGURATION | Authentication | Choose between the Certificate and a pre-shared key |
| Certificate (rsa-sig) | ||
| Pre-shared Key | ||
| Certificate Authority ID | Issuer DN (required) | |
| Local ID | Gateway subject DN | |
| Remote ID | Workload subject DN | |
| Idle Timeout (minutes) | e.g. 5 | |
| Rules | Rules include Protected IP list. Scope is expanded to all workloads when not restricted to specific labels. |
Requirements for Certificate Setup on Workloads
To use PKI certificates with SecureConnect, you must independently set up certificates on your Windows and Linux workloads.
Generate or obtain certificates from a trusted source in your organization. You should only use certificates obtained from trusted sources.
File Requirements
|
File |
Requirements |
|---|---|
|
Issuer's certificate |
The global CA certificate, either root or intermediate, in PEM or DER format NOTE:
On Linux, the issuer's certificate must be readable by the Illumio user. |
|
pkcs12 container |
Archive containing the public key, private key, and identity certificate generated for the workload host. Sign the identity certificate using the global root certificate. You can password protect the container and private key but do not password protect the public key. |
Certificate Requirements
There are certain requirements regarding certificate use that you have to follow for the installation:
-
x509 certificate must contain fields
SubjectNameandSubjectAltName. -
SubjectNameDN should contain CN, which has to match to DNS name ofSubjectAltName.
X509v3 Subject Alternative Name: DNS:centos6, email:centos6@ilabs.io Subject: OU=VEN, CN=centos6.ilabs.io
-
x509v3 extension with the key usage must have Digital Signature, Key agreement
-
x509v3 extension with extended key usage must contain either "Any Extended Key Usage" or "IPSec End System, IPSec User, TLS Web Server Authentication"
-
x509v3 extension with the authority Key Identifier field is required as well
Installation Locations
Windows Store
Use the Windows OS, for example Microsoft Management Console (MMC), to import the files into these locations of the local machine store (not into your user store).
- Root certificate: Trusted Root Certificate Store
- pkcs12 container: Personal ("My") certificate store
/My/Personal contains more than one certificate issued by the same issuer, Windows doesn’t know what to pick to program Cert for SecureConnect.Linux Directories
Copy the files into the following Linux directories. (You cannot change these directories.)
- Root certificate:
/opt/illumio_ven/etc/ipsed.d/cacert - pkcs12 container:
/opt/illumio_ven/etc/ipsed.d/private
Enable SecureConnect for a Rule
The following table lists the valid provider and consumer combinations for which you can enable SecureConnect:
|
Provider |
Service |
Consumer |
|---|---|---|
|
Workload |
Any service |
Workload |
|
All workloads |
Any service |
All workloads |
|
Label/Label Group |
Any service |
Label/Label Group |
SecureConnect is supported on workloads in Visibility Only and Full enforcement states.
When SecureConnect is enabled on a VEN, it is not disabled when the VEN is suspended.
From the PCE web console menu, choose Rulesets and Rules > Ruleset.
The Rulesets page appears.
When you enable SecureConnect for a rule, the PCE duplicates symmetrical encryption for both sides of the connection.