This section describes the concepts of role-based access control (RBAC) and how it works with the PCE.
Overview of Role-based Access Control
Security-oriented companies should grant employees the exact permissions they need based on their role. Illumio Core uses role-based access control (RBAC) to deliver security at an enterprise scale in the following ways:
-
Assign your users the least required privilege they need to perform their jobs.
Limit access for your users to the smallest operation-set they need to perform their jobs; for example, monitor for security events.
-
Implement separation of duties.
Delegate the responsibility to manage a zone to a specific team or delegate authority to application teams; for example, delegate a team to manage security for the US-West Dev zone, or assign the DevOps team to set security policy for the HRM application they manage.
-
Grant access to users based on two dimensions: roles and scopes.
Each role grants access to a set of capabilities in Illumio Core. Scopes define the workloads in your organization that users can access and are based on three labels: Application, Environment, and Location. The scopes specify the boundaries of the sphere of influence granted to a user.
For example, a user can be added to the Ruleset Provisioner role with the scope Application CRM, Environment Staging, and Location US. With that access, the user could provision rulesets for workloads that are part of your CRM application in the Staging environment located in the US.
-
Centrally manage user authentication and authorization for Illumio Core.
Configure single sign-on with your corporate Identity Provider (IdP) and designate which external IdP groups should have access roles. Group membership is managed by your IdP while resource authorization is configured in Illumio Core.
Use Cases
Illumio designed our RBAC feature around a set of use cases based on the way that enterprises manage the security of the computing assets in their environment. These use cases encompass common security workflows for the modern, security-conscious enterprise. The personas include different levels of security professionals.
Support the Security Workflow
Customers can configure the RBAC feature to support any type of responsibility bifurcation that they have in their workflow models. For example, the following workflows are supported:
- Architect-level professionals define all security policy for an enterprise by adding rulesets and rules in the PCE.
- Junior-level professionals provision rulesets and rules to workloads during maintenance windows. Junior personnel cannot edit any policy items in the Illumio PCE.
- Some users only view the infrastructure and alert senior team members when security issues occur.
Manage Security for Specific Workloads
When you combine Illumio Core RBAC roles with scopes, you can secure access for IT teams who support specific applications or different geographic locations. For example, customers could delegate authority for workloads in the following ways:
- To manage security for workloads around silos; for example, a particular cloud provider like AWS.
- To decentralize their security policy to specific application teams allowing them to act quickly when managing application security without waiting for the central security team.
- To bifurcate the security of their infrastructure in such a way that one user is responsible only for the West coast assets and another user is responsible for the East coast assets.
Features of Role-based Access Control
Built-in Roles
Illumio Core includes seven roles that grant users access to perform operations. Each role is matched with a scope. See About Roles, Scopes, and Granted Access for information.
Granular Permissions
You can assign multiple roles to one user and by mixing and matching the different roles, you can achieve different levels of granularity of permissions.
You can grant different permissions to different users for different resources by defining scopes. For example, you might allow some users complete access to add rulesets for all workloads in your staging environment. For other users, you might grant access to all workloads in all environments. Users can be assigned exactly one role, representing their singular job function while other users can be assigned multiple roles, representing multiple job functions.
Identity Federation Using External Users and Groups
You can connect to external LDAP directories to manage users and user groups by configuring single sign-on (SSO) for the PCE.
Using this feature, you can create and manage users locally in PCE, or use an IdP to manage users and user groups from an existing directory. External user and user groups authenticate with the external IdPs.
Custom Role Assignments
You can customize access to suit your organization by specifying specific scopes for the Ruleset Manager and Ruleset Provisioner roles.
Audit Information
You can access an audit trail of user activity through the following reports:
- The User Activity page, which displays the authentication details for each user, when they logged in, and whether they are online.
- The Organization Events page, which displays when Organization Owners granted users access, when users logged in and out, and the actions they performed.
About Roles, Scopes, and Granted Access
Illumio Core includes seven roles that grant users access to perform operations. Each role is matched with a scope. You can add users (local and external) and groups to all the roles.
Roles with Global Scopes
These Global Roles use the scope All Applications, All Environments, and All Locations. You cannot change the scope for these roles. The roles have the following capabilities in Illumio Core.
| Role | Granted Access |
|---|---|
| Global Organization Owner | Perform all actions: add, edit, or delete any resource, security settings, or user account |
| Global Administrator | Perform all actions except user management: add, edit, or delete any resource or organization setting |
| Global Read Only | View any resource or organization setting They cannot perform any operations. |
| Global Policy Object Provisioner |
Provision rules containing IP lists, services, and label groups They cannot provision rulesets, virtual services, or virtual servers, or add, modify, or delete existing policy items. |
You can add, modify, and delete your API keys because you own them.
About the Read Only User Role
The Read Only User role applies to all users in your organization—local, external, and users who are members of external groups managed by your IdP. This role allows users to view resources in Illumio Core when they are not explicitly assigned to roles and scopes in the PCE.
For example, you configure single sign-on for your corporate Microsoft Active Directory Federation Services (AD FS) so that users managed by AD FS can log into the PCE by using their corporate usernames and passwords. However, you haven't added all your external users to the PCE or assigned them to roles. These users can still log into the PCE by authenticating with the corporate IdP and view resources in the PCE.
The Read Only User role is not listed in the Role-Based Access > Global Roles or Scoped Roles pages because it is considered a default, catchall type of role. Users have access to this role on an organization-wide basis because you either enable or disable it for your entire organization. Additionally, you do not see it in the list of a user's role assignments when you view the user's details page (Role-Based Access > Users and Groups). However, when the role is enabled for your organization, you see it listed in the Role-Based Access > User Activity details for each user.
You can enable and disable the Read Only User role from the Role-Based Access > Global Roles > Global Read Only page.
When the Read Only User role is disabled for your organization, users who are not assigned to roles cannot access Illumio managed resources. When attempting to log into the PCE, they are still authenticated by their corporate IdP but the PCE immediately logs them out because they do not have access (even read-only access) to any Illumio managed assets.
Roles with Custom Scopes
You can apply the following roles to specific scopes. These roles are called “Scoped Roles.”
| Role | Granted Access |
|---|---|
| Full Ruleset Manager |
|
| Limited Ruleset Manager |
|
| Ruleset Provisioner |
Provision rulesets within specified scope. NOTE:
You can choose the All Applications, All Environments, and All Locations scope and custom scopes with the Ruleset Provisioner role. |
| Workload Manager |
Manage workloads and pairing profiles within the specified scope. Read-only access provided to all other resources. NOTE:
The 19.1.0 PCE does not support unpairing multiple managed workloads via the REST API when you are logged in as a Workload Manager. You can unpair workloads using the PCE web console because it restricts selection of workloads by the user's scope. However, via the REST API, the bulk unpair operation fails when multiple workloads are selected and one or more of the workloads are out of the user's scope. |
Workload Manager Role
Use Case 1
You want to use scripts in your development environment to programmatically spin up and bring down workloads; your scripts create pairing profiles and generate pairing keys without you granting elevated Admin privileges to the scripts.
Use Case 2
Your application teams are in charge of changing the security posture of workloads, such as changing the policy enforcement states. You want to allow your application teams to manage workload security without granting them broad privileges, such as All | All | All access.
Use Case 3
You want to prevent your PCE users from accidentally changing workload labels by moving the workloads in Illumination.
Solution
Users with the Workload Manager role can create, update, and delete workloads and pairing profiles. This role is a scoped role; when you assign a user to a scope, they can only manage workloads within the allocated scope. The Workload Manager can pair, unpair, and suspend VENs and change the policy state. It is an additive role; you can assign the Workload Manager role to a user and combine it with any other PCE role to provide additional privileges for that user.
Configuration
- Create a local user with “None” or Global Read Only role.
- Assign the Workload Manager role to the user.
- (Optional) Provide the invitation link to the new workload manager user.
- The workload manager can then log into the PCE and manage workloads and pairing profiles per the allocated scope.
The Workload Manager role is available under Scoped Roles. Users assigned this role can view applications that are outside their scopes but can only modify those applications that are within their scopes.
A workload manager user cannot clear traffic counters from workloads within their scope.
Example: Limited Ruleset Manager Role
A user has the role Full Ruleset Manager role and access to the following scope:
All Applications | Production Environment | All Locations
The user can create and manage:
- Any ruleset that matches the Production environment
-
Intra- or extra-scope rules that match this scope:
All Applications | Production Environment | All Locations
Where the provider and consumer of the rule are both within the Production environment scope.
For intra-scope rules, all workloads can communicate within their group (as defined by the scope), so the rule consumer is not restricted. However, in extra-scope rules, the Environment label of the resource selected as the consumer must match the label in the scope exactly.
The user cannot create a rule with the scope “All | All | All” because that scope is broader than the user's access, which is only for the Production environment.
Because the user is a member of the Limited Ruleset Manager role, the user cannot manage custom iptables rules and the following resources cannot be selected as consumers in extra-scope rules:
- IP lists
- Label groups
- User groups
- Workloads
Combine Roles to Support Security Workflows
Illumio includes fine-grained roles to manage security policy. The roles control different aspects of the security workflow. By mixing and matching them, you can effectively control the access needed by your company.
Ruleset Only Roles
You can add users to the Full Ruleset Manager and Ruleset Provisioner roles so that they can edit the security policies on the workloads within their assigned scopes without affecting other entities, such as services, virtual services, or virtual servers.
These users can write rules for their workloads and provision them when the rules do not have dependencies on global objects, such as services or IP lists.
Ruleset Plus Global Policy Object Provisioner Roles
You can add users to the Ruleset Manager (Full or Limited) role and the Global Policy Object Provisioner role so that they can control the security policy for workloads.
These users can create rulesets within their assigned scopes and write rules that are not dependent on global objects. However, they can provision any workloads, even those containing services, IP lists, and label groups.
Global Organization Owner or Administrator Roles
You can add architect-level professionals to the Global Organization Owner or Global Administrator role so that they can define all security policy for an enterprise.
They have the capability to modify global objects, such as services and labels, add workloads, pair workloads, and change workload modes to function as a security policy administrator.
Role Access is Additive
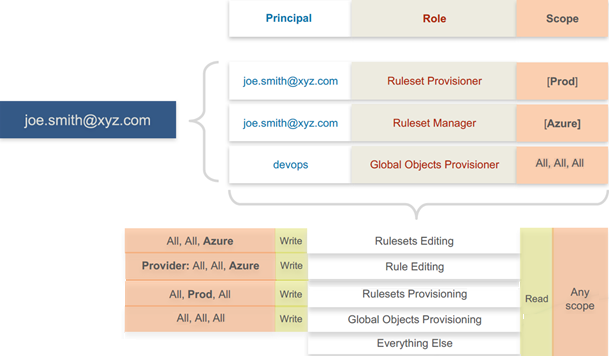
In the following example, Joe Smith is added to two user roles and one external group and each is assigned a specific role and scope. Joe's ability to manage security for his company is a union of the roles and scopes he is assigned to.
Example Role Workflows
The following example shows the hand offs between a user who is a member of the Global Organization Owner role and a member of a Ruleset Manager role.
- An Organization Owner grants access to one or more scopes for a Ruleset Manager by selecting specific labels, which define the permitted scopes for the Ruleset Manager.
- The Ruleset Manager logs in and creates rules that conform to the specified scopes, as defined by the labels that are accessible to that user.
- The Ruleset Manager has read-only access to all other PCE resources, such as services or rulesets with different scopes from the scopes that the Ruleset Manager can access.
- The Organization Owner reviews the rules created by the Ruleset Manager and provisions them as needed.
Prerequisites and Limitations
- You must be a member of the Global Organization Owner role to manage users, roles, and scopes in the PCE.
-
Configuring SSO for an Illumio supported IdP is required for using RBAC with external users and groups. See Authentication for information.
If you have not configured SSO, you can still add external users and external groups to the PCE; however, these users will not be able to log into the PCE because they will not be able to reach the IdP or SAML server to authenticate.
- Illumio resources that are not labeled are not access restricted and are accessible by all users.
-
External users who are designated by username and not an email address in your IdP will not receive an automatic invitation to access the PCE. You must send them the PCE URL so they can log in.
- You cannot change the primary designation for users and groups in the PCE; specifically, the email address for a local user, the username or email address for an external user, or the contents of the External Group field for an external group. To change these values, you must delete the users or groups and re-add them to the PCE.
-
An App Owner who is in charge of the application in both production and development environments does not have permissions to write extra-scope rules between production and development.
Local users are not locked out of their accounts when they fail to log in. After 5 consecutive failures, the PCE emails the user that their account might be compromised.
Locked users retain all their granted access to scopes in the PCE; however, they cannot log into the PCE.